The internet is a vast space where near endless information is stored, shared and processed.
WHAT IS TWO-FACTOR AUTHENTICATION?
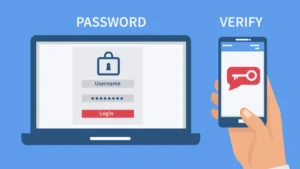
Two-factor authentication (2FA) is a specific type of multi-factor authentication (MFA) that strengthens access security by requiring two methods to verify your identity. It is otherwise referred to as two-step verification or dual-factor authentication, is a security process in which users provide two different authentication factors to verify themselves before access is granted.
2FA provides a higher level of security than single-factor authentication (SFA), in which the user provides only one factor such as a password. 2FA methods typically require a user password as the first factor accompanied with and a second, different factor either a security token or a biometric factor, such as a fingerprint or facial scan.
IMPORTANCE OF 2FA
2FA creates an additional layer of security by making it harder for hackers to gain access to a person’s device or online accounts. In the event that the victim’s password is hacked the account is protected by the second authentication.
2FA combats the fraudulent practice of sending emails or other messages purporting to be from reputable companies in order to induce individuals to reveal personal information, such as passwords and credit card numbers also known as phishing. 2FA also protects against vicious password attacks and secures users’ logins from attackers.
HOW TO ENABLE 2FA
The enablement can vary based on the device or application. However, generally 2FA processes involve the following:
- Open the application or the website.
- Enter username and password.
- Initiate the second login step, usually an information that can only be provided by the specific user such as biometrics, a security token and an ID card.
- Enter the one-time code generated.
- Access is granted to the application or website.
FACTORS OF AUTHENTICATION
Factors are the pieces of information a user can provide to verify their identity. There are five factors of authentication used by security professionals and they are as follows:
Knowledge Factor
The knowledge factor verifies identity by requesting information only an individual user would know. The most common example is a password.
Possession Factor
The Possession factor verifies the identity of a user by requiring proof of information that only the user should possess. Tokens are a commonly used possession factor of authentication.
Inherence Factor
Inherence factor of authentication verifies the identity of a user by confirming attributes that would belong only to that user, such as face recognition and fingerprint which is unique to individuals.
Location Factor
The location factor of authentication confirms the identity based on their location in the world. If a user has registered an account in one country, he will be notified of any login attempts from another location. It is based on the IP address of the original location.
TYPES OF 2FA
- Short Message Service Two-Factor Authentication (SMS 2FA): SMS 2FA validates the identity of a user by texting a security code to their mobile device. The user then enters the code into the website or application to gain access to the information. SMS 2FA sends a One-Time password (OTP) to a user’s device. SMS 2FA requires that users disclose their phone numbers, however it can make some people uncomfortable because it raises concerns around privacy.
- Time-Based One Time Password (TOTP) Two Factor Authentication 2FA: TOTP 2FA generates a key locally on the device a user is attempting to access. The security key is a QR code scanned with typically a mobile device to generate a series of numbers. The user then enters those numbers into the website or application to gain access.
CONCLUSION
Programmes with just the single-factor authentication, usually the password, may not be optimally effective. The option of adopting a double layer of cyber security (2FA method) provides greater assurance of the safety of devices. The relative effectiveness of this self-activated, user-friendly security measure has resulted in individuals and organizations alike across industries implementing the system. It is therefore strongly recommended that all users of the internet should embrace 2FA.